
Global Data Exfiltration Market Size, Trends & Analysis - Forecasts to 2026 By Component (Solutions, Services), By Organization Size (Small and Medium-sized Enterprises (SMEs), Large Enterprises), By Vertical (BFSI, Government and Defense, Retail and eCommerce, IT and Telecom, Healthcare and Life Sciences, Manufacturing, Energy and Utilities, Others [Travel and Hospitality, Media and Entertainment, and Education], End-User Landscape, Company Market Share Analysis, and Competitor Analysis
Data Exfiltration is also known as data extrusion. Data exfiltration is a confidentiality violation that happens when an organization's confidential information is transmitted or copied without permission from a server or computer to a location managed by a malicious user. It is primarily a deliberate attack in which the main purpose of the hacker is to copy and extract important information from the database. Via remote applications or directly downloading a portable media system, hackers get information about the target server. A company's medical records, personal liberty or confidential information, and financial details, personal information data, including bank account or credit card details, are some of the other major privacy thefts.
Since companies continue to depend upon digital data and web applications to carry out their everyday operations over the years, the increasing database of personal and financial data is maintained in clouds that end up leaving individuals and company entities liable to future liability related to safety failures. Increasing protection needs by the rapid growth of mobile users would contribute to growth in the global data exfiltration market. Additional factors are expected to drive growth in the global data exfiltration market - growing cybersecurity threats of confidential information theft and the increased request for cybersecurity solutions. Also, rising data loss issues in the on-site setting are expected to contribute to target market sales increase.
Large enterprises are focused on partnering with different players to digitize in developed countries and satisfy the increasing need for cloud-based data security services. This is one of the latest developments observed in the global data exfiltration market, which is currently ongoing.
Major drivers of the data exfiltration industry are internet fraud, internet misuse, and data leak complexity. As specialized cyber threats to valuable information theft are on the upswing, the data exfiltration market is expected to gain momentum in the coming years. Furthermore, the market for cybersecurity solutions is expected to rise during the forthcoming years. Several organizations are implementing network security technologies with the assistance of their regional council. For instance, the UK Government has taken a variety of measures to detect and prevent data misuse. To monitor how well the records are managed and the degree of security needed to avoid trivial exfiltration, information isolation, net segregation, and adoption of honeypots, organizations have to enforce and even distribute defensive marks to the information. Organizations around the globe are tackling the challenge of data exfiltration by using several approaches, such as timely detection of exfiltration attempts, as well as the implementation of retroactive detection of leakage to avoid repeated damage and to assess the effects by detecting individual losses.
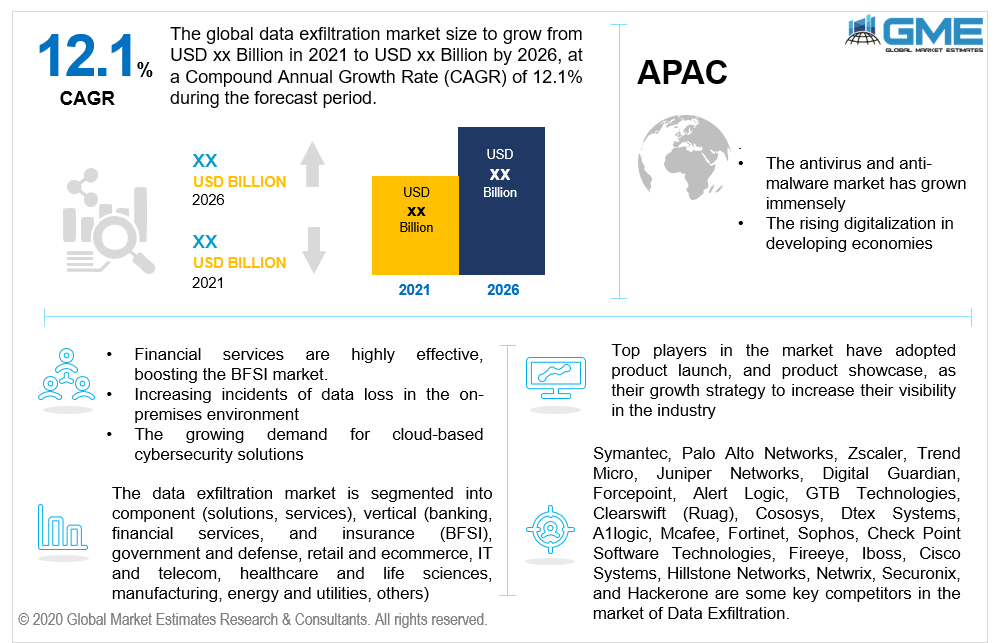
Based on the component, the market is divided into solutions and services. During the forecast timeframe, the antivirus/anti-malware segment is anticipated to hold the largest share in the market in terms of revenue. Antivirus software is a collection of applications, identifying, avoiding, and eliminating cyber-attacks from viruses. Anti-malware is a program that detects, inhibits, and fixes the caused by malicious codes in a device. These programs prevent, track and eradicate harmful activities like computer viruses, root-kits, ads, spyware, and hackers. In recent years, the antiviral / anti-malware segment has expanded immensely since operations in the business and customer fields are easy.
As per the organization size, the data exfiltration market is segmented into small and medium-sized enterprises (SMEs), and large enterprises. The fast-growing segment will be the mid-size companies (SMEs). Some SMEs rely on avoiding attacks from accessing the system rather than identifying and blocking data penetration and usually opt for activities such as buying more security devices and engaging in employee safety training. Furthermore, employees of small and medium-sized enterprises owing to a shortage of security preparation are susceptible to human and procedural deficiencies, such as the inability to retain security certifications, which certainly make data exfiltration simpler.
Based on the vertical, the data exfiltration market is classified into BFSI, government and defense, retail and e-commerce, IT and telecom, healthcare and life sciences, manufacturing, and energy & utilities, among others. The BFSI vertical segment is projected to rise at a fast pace in the coming years. The increasing rate of growth is due to increased smartphones and digital banking activities. Companies in the BFSI industry that offer banking and financial services, including core banking, private banking, investment banking, and cards, as well as mutual funds, payment gateways, and stockbroking are highly reliable, pushing through the coming years. Insurance-related companies are also included. Cloud and data centers have been the backbone of the BFSI industry since the digital technology revolution.
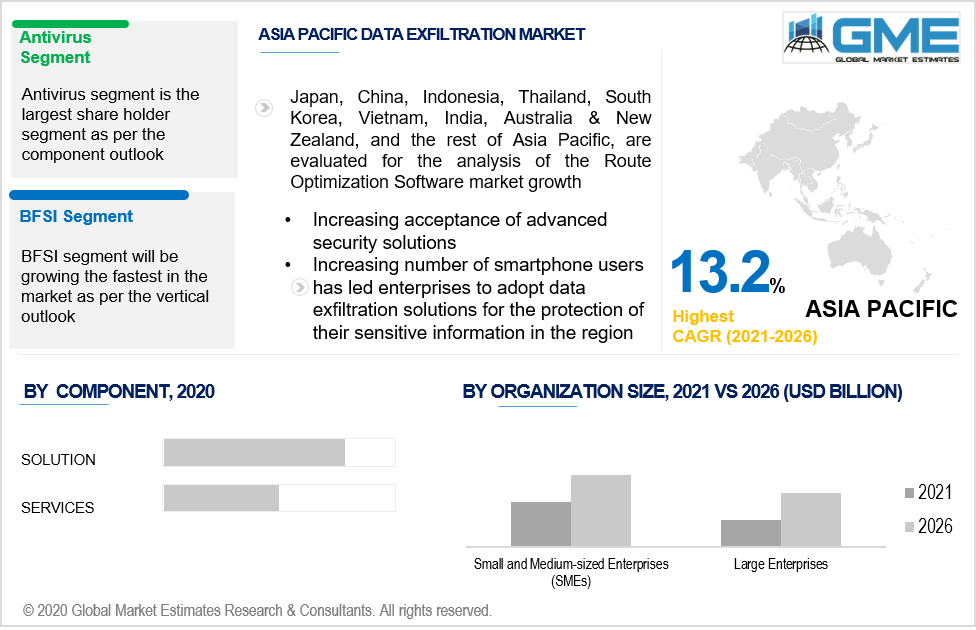
As per the regional analysis, the market is classified into North America, Asia Pacific, Europe, Middle East & Africa, and Central & South America. The growing demand for worldwide network traffic protection and increasing use of smart devices, such as telephones, laptops, and other regional utilities, are projected to increase North America's share of the market. The demand for data exfiltration in North America is also driven by other factors such as extending the internet retail and vertical banking, growing use of cloud storage, and increasing importance of legal enforcement. Furthermore, owing to the huge demand from the information technology & telecom segments, the Asia-Pacific region is projected to rise at a faster growth rate over the predicted timeframe.
Symantec, Palo Alto Networks, Zscaler, Trend Micro, Juniper Networks, Digital Guardian, Forcepoint, Alert Logic, GTB Technologies, Clearswift (Ruag), Cososys, Dtex Systems, A1logic, Mcafee, Fortinet, Sophos, Check Point Software Technologies, Fireeye, Iboss, Cisco Systems, Hillstone Networks, Netwrix, Securonix, and Hackerone are some key competitors in the market of Data Exfiltration.
Please note: This is not an exhaustive list of companies profiled in the report.
In February 2020, McAfee and DXC Technology entered into a strategic collaboration and unveiled the global MDR app. Both MDR systems can be used by DXC Technologies to identify and fix consumer protection problems more easily and effectively. The platform includes advanced threat and response data points, as well as surveillance, forensics, and research.
We value your investment and offer free customization with every report to fulfil your exact research needs.
The Global Data Exfiltration Market has been studied from the year 2019 till 2026. However, the CAGR provided in the report is from the year 2021 to 2026. The research methodology involved three stages: Desk research, Primary research, and Analysis & Output from the entire research process.
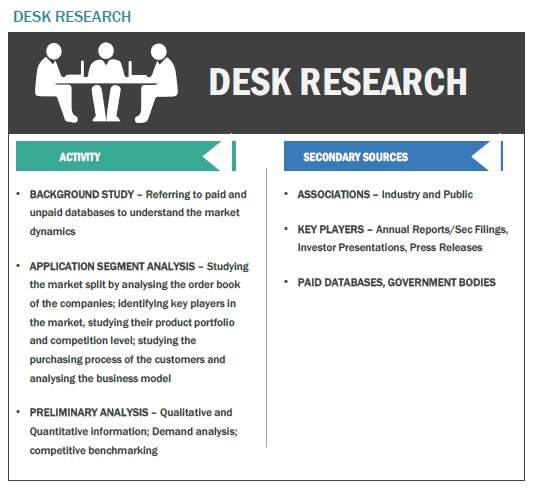
The desk research involved a robust background study which meant referring to paid and unpaid databases to understand the market dynamics; mapping contracts from press releases; identifying the key players in the market, studying their product portfolio, competition level, annual reports/SEC filings & investor presentations; and learning the demand and supply-side analysis for the Data Exfiltration Market.
The primary research activity included telephonic conversations with more than 50 tier 1 industry consultants, distributors, and end-use product manufacturers.
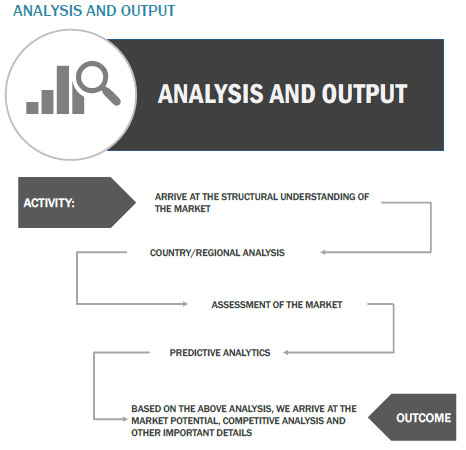
Finally, based on the above thorough research process, an in-depth analysis was carried out considering the following aspects: market attractiveness, current & future market trends, market share analysis, SWOT analysis of the company and customer analytics.
Tailor made solutions just for you
80% of our clients seek made-to-order reports. How do you want us to tailor yours?
OUR CLIENTS